Why You need to install Antivirus on Mac and iOS Devices

Over the years, Apple devices have proven to be more secure than their Windows and Android cousins, as a PC user of many years, I vividly remember the cloak of invincibility that Apple users bragged about. They looked down on us, wondering what all the antivirus fuss was about.
The perception of security has made many Apple users skeptical about antivirus, and for a while even the vendors seemed to focus more on Windows Operating Systems. This has not changed much, however, as more exploits chink the famous Apple cloak of invincibility Apple users are suddenly asking themselves whether they need any additional security for their devices, and antivirus vendors have better security offerings for Apple.
The stark reality is that there is no IT system that is 100% secure, sorry Apple users, it is the truth. There are ways to make your Apple devices more secure, out of the abundance of caution, and finally for the same reason you would lock gate and lock your front door, I would also recommend an extra layer of security software for your beloved Apple device.
As the number of Apple exploits increases it is time to consider beefing up your device security, here are a few facts to support our recommendation:
1. The number of attacks on Apple devices has increased.
a. As of July 2021, we are on the 13th Zero-day vulnerability detected in Apple Operating Systems. The vulnerability with CVE-2021-30807 was reported anonymously to Apple and is described as a memory corruption flaw that could be exploited to launch remote code execution attacks with kernel privileges.
2. Then there is the Wi-Fi Hack, which makes all iPhones vulnerable to attack. As reported by BeepingComputer, simply connecting to certain Wi-Fi SSID names, it can make you think that you are giving it instructions and attempt to execute those instructions. In this instance the SSID name was “%p%s%s%s%s%n”, this made the iPhone think that the name was a command to execute rather than a simple name.
3. Then there is the NSO hack, which Amnesty International said it discovered and iPhones could be compromised with data stolen without the phone owner even having to click on a link. So, without any intervention on your part, the hack makes it possible for the attacker to access the content on your phone – your messages, emails, microphone, and camera.
4. iOS 14.7.1 is the highest number of iOS versions that have ever reached with most updates required by exploits and detected vulnerabilities.
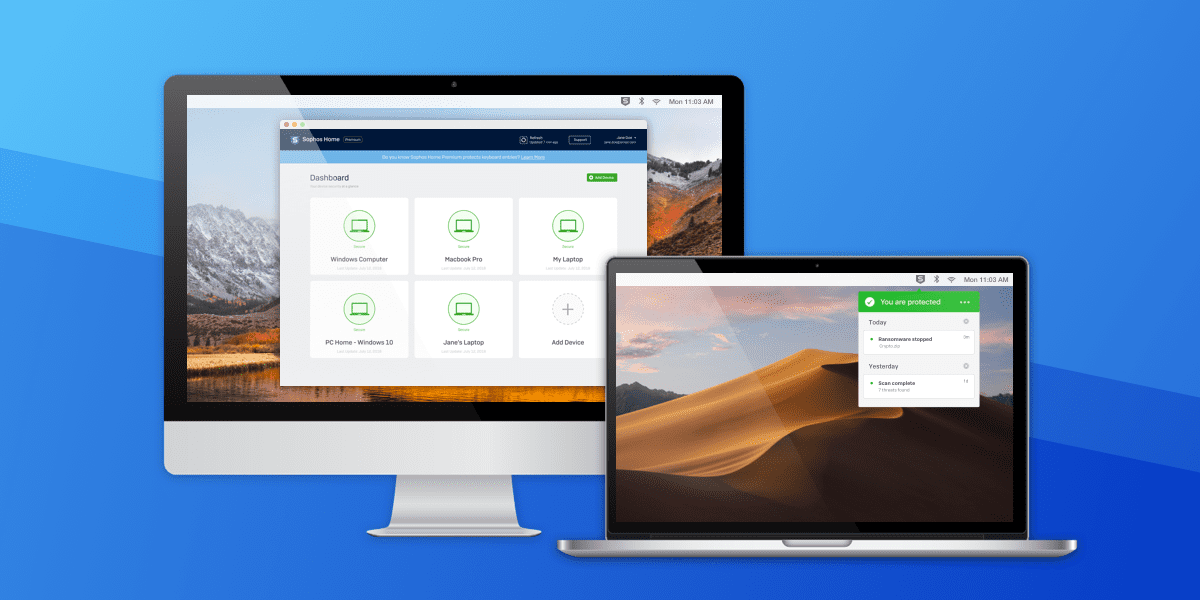
From the exploits discussed, it is highly recommended to have antivirus with a Firewall installed on your Apple devices (MacOS & iOS) to prevent these exploitations. To learn more and get the best protection for your Apple devices, click here for further information.
Additionally, implement the following guidelines to improve the overall security of your Mac and iOS devices
1. Avoid Jailbreaking your iPadOS and iOS; this makes you extremely vulnerable to attacks
2. Always update your MacOS, iPadOS & iOS. Apple often releases patches to fix vulnerabilities in the OS. Never leave your device to run on outdated OS.
3. Turn off “Ask to Join Networks” settings and set “Auto-Join Hotspot” to never.
4. Update firmware and Apps regularly. As Apple fixes vulnerabilities in the OS, Apps and other firmware developers also update their products to improve security so ensure to stay up to date.
5. Create restricted user account on MacOS devices for day-to-day activities. Standard day-to-day user accounts have less privileges to run apps, install, and perform other tasks. This ensures that when your device is compromised, it becomes challenging for the hacker to perform privileged escalation and hence will require root permission to exploit the vulnerabilities.
6. Use Strong Passwords: Use strong passwords and different passwords for standard day-to-day accounts and superuser accounts. This will ensure when a standard user account is compromised, the hacker cannot run malware with your superuser privileges.
7. Enable Mac Firewall. MacOS ships with a built-in Firewall but it is not enabled by default. You can enable this from Security & Privacy from System Settings. The Firewall will block illegitimate inbound and outbound connections.
8. App Store: Only download and install Apps from the App Store. Ensure Apps cannot be downloaded and installed from Anywhere. Only install Apps from the App Store.